Customer verification at Zerodha
With the rise of online platforms giving instant loans completely digitally, online identity fraud has skyrocketed. Several have been in the news recently for lax checks and improper KYC (Know Your Customer) practices that allowed fraudsters to use manipulated images of PAN cards and other documents belonging to the victims of identity theft to avail loans with great ease. In the very competitive landscape of digital lending, the quest to show fast user growth has meant that some companies have compromised KYC checks prescribed by regulations.
Loans taken by fraudsters with the intent to default not only put the financial liability on the person whose identity is stolen but also hurts their credit score. Thankfully, in the stockbroking world, identity theft isn’t as big a problem because no money is lent to a customer and any fund transfer only happens to verified bank accounts. We have heard of cases in the industry where fraudsters created false identities using the PAN of another person to avoid paying income taxes on capital market gains.
The uproar on social media on this matter has resulted in a number of our concerned customers writing to us asking whether something like that could happen to them at Zerodha. This post explains in detail the checks and processes that we employ when onboarding a new customer, even beyond the ones prescribed by regulations. In addition, our processes and systems are regularly audited by multiple regulatory bodies and internal and external auditors.
When a new customer signs up online with us, the three most important checks are:
- Verifying the authenticity of their identity and address proofs.
- Verifying that the bank account really belongs to the customer.
- Verifying that the person opening the account online is the one in the proofs.
Validating documents
When a user starts the onboarding process, first, their mobile number and e-mail address are verified by sending OTPs.
1. Obtaining PAN
The customer enters their date of birth and PAN (number), and we fetch the details of the PAN, including their legal name, from the Income Tax Department’s systems in real-time. We do not ascertain the validity of a PAN-based on an uploaded photocopy.
2. Obtaining Proof of Identity (POI) & Proof of Address (POA)
We obtain a digitally signed copy (in machine-readable form) of the customer’s Aadhaar directly from UIDAI via the DigiLocker.gov.in portal (Govt. portal for storing and sharing authenticated, digitally signed documents) once the customer logs in and consents to share. DigiLocker logins are based on Aadhaar verification and SMS OTPs via the mobile linked to Aadhaar. We do not obtain the actual Aadhaar number as prescribed by the law.
3. Verifying PAN against Aadhaar.
At this point, the customer has not uploaded any documents. They have been obtained directly from govt. systems, establishing the authenticity of the documents. Letting customers upload photos of PAN, Aadhaar, or other identity proofs and using them for verification is a flawed process as those can be easily manipulated.
The next step is to verify the name and date of birth on the PAN obtained from the IT Department against the name and date of birth on the Aadhaar obtained from DigiLocker. This check is done both by an automated system and human verifiers. This one critical step significantly reduces the probability of easy identity theft as seen in lending platforms.
4. Verifying the bank account.
A customer has to explicitly link one or more bank accounts they own to their trading account. SEBI regulations mandate that fund transfers (paying in to fund the trading account or withdrawing the trading balance) are only to be allowed to be linked, verified bank accounts. This, again, significantly reduces the probability of fraudulent fund withdrawals.
We collect the customer’s bank account number and IFSC code and do a “penny drop” (sending a few paise) to their bank account to ensure that it is a valid account. The bank systems return the name of the account holder, which is then verified against the name on the PAN (obtained earlier from the IT Department’s systems) using both automated and human checks. If the customer opts for a UPI-based verification, the banking systems are again used to verify that the UPI ID is linked to the original PAN.
This establishes that the bank account really belongs to the person whose name PAN and Aadhaar are in.
5. Supporting documents.
We obtain copies of supporting documents depending on the kind of accounts they open, for example, bank statements, canceled cheques, etc., whose details are verified against the validated bank account by automated systems and human verifiers.
The customer is now asked to upload a copy of their ePAN (generated from the Income Tax Department’s portal) or a copy of their physical PAN. This merely acts as an additional check for a better audit trail to the PAN data that has already been obtained and verified from the Income Tax Department’s systems.
6. In-person verification (IPV – Video KYC).
At this point, the authenticity of the documents and the bank accounts are verified as they have been obtained directly from their issuers various govt. departments and banks. Since DigiLocker involves mobile (OTPs) that are linked to Aadhaar, it is also established that whoever is opening the account has access to the mobile device linked to the original documents.
IPV helps establish that the person who is going through the account opening flow is really the person who the original proofs and the linked mobile number belong to. To do this, we generate a short-lived numeric OTP and send it to the customer’s mobile. They write the OTP down on a piece of paper and appear in front of their webcam to do a video KYC.
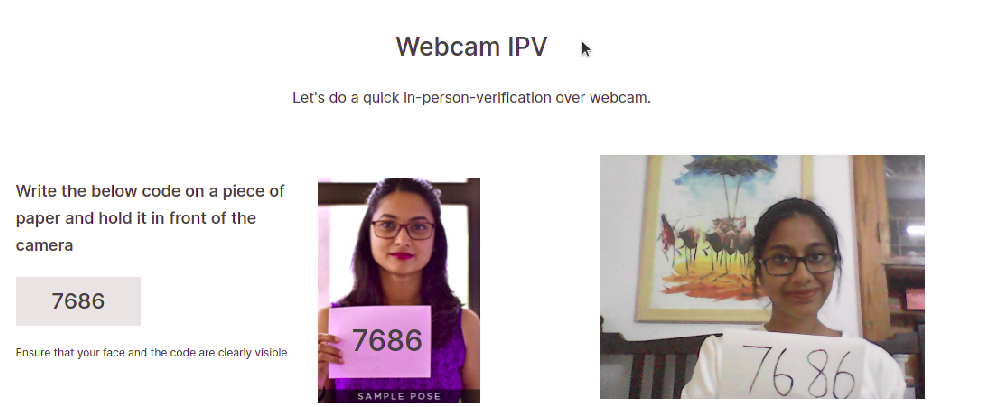
IPV
We record a short video clip of the customer while they are doing the IPV. Three important things happen here:
- The short-lived, handwritten OTP ensures that it is not a pre-recorded clip. If someone goes to extreme lengths to manipulate a pre-recorded video clip and insert a handwritten OTP using video manipulation within the brief period of time when the OTP is valid, it establishes a clear audit trail of the intent to defraud.
- Our systems do an automated face match between the IPV video clip, the Aadhaar photo obtained from DigiLocker, and the secondary copy of the PAN or ePAN the customer uploaded.
- All these are verified by systems and again by human verifiers.
Although regulations do not mandate IPV for KRA verified customers (already KYC verified at another broker) or customers opening accounts via Aadhaar/UIDAI authentication, we do this for all customers regardless as it is a critical step in verifying identity and liveness during online onboarding.
7. eSign (digital signature).
The final step in the account opening process is the act of the customer digitally signing (IT Act, 2000) the account opening PDF document, which collates all the information, proof, and documents they have submitted, legally ratifying the submission and various declarations and terms as prescribed by regulations. The customer digitally signs the PDF via Digio, a frontend to the Aadhaar/UIDAI based digital signature confirmed via an SMS OTP to the mobile linked to the customer’s Aadhaar. Once the customer digitally signs the document, the name on the cryptographic digital signature is verified against the name on the ID proof that was originally obtained from DigiLocker, ensuring that the owner of the digital signature is the same person as the one verified in the previous steps. Again, this is a critical step. This also leaves a strong audit trail for the customer, Zerodha, and the regulator to verify the provenance of the account opening agreement and the documents involved in it.
8. Standard measures.
All the checks described above are done at multiple levels, using automated systems as the first line of check, and verification by multiple human checkers (a maker-checker system). There are also periodic quality checks and regular internal audits of random samples to ensure that these checks and processes continue to run as designed.
In addition, standard measures such as recording audit trails of the account opening processes, including IP addresses, are employed. If a mismatch is found, like the geographic IP location not matching a customer’s country of residence in the proof of address, a flag is raised.
Moreover, once an account is opened and customers start trading and investing, the trading activity passes through multiple comprehensive checks that raise flags for trades of fraudulent nature, money laundering checks (PMLA), etc., as prescribed by regulations. For instance, a common check is comparing the volume of trading activity against the annual income range declared by the customer during the onboarding.
For customers, we offer strong 2FA (TOTP) on their accounts and instantly notify them of logins to their accounts from unusual geographic locations. The Nudge system blocks dubious-looking trades from being executed, which significantly reduces the incentive for scammers to commit fraud in trading accounts via common means such as trading using highly illiquid derivative instruments.
In addition, the SEBI regulation that instituted a mandatory SMS OTP verification on selling shares (debiting stocks from a demat accounts) at the depository level has almost entirely eliminated the possibility of a customer’s securities being moved from their demat account without their knowledge at the hands of not just third parties, but brokers themselves.
The effectiveness of these checks.
Each of these checks and security measures reduce the probability of fraud by a significant degree. While none of them individually are foolproof, combining all of them together is a highly effective way of reducing the ease of doing fraud. No anti-fraud system can guarantee 100% efficacy, but a cautious and holistic approach can reduce the probability of fraud to a small fraction. Over the years, we have instituted measures over and above what regulations prescribe to reduce the vector for many kinds of frauds. It is unfortunate that companies forgo caution and checks and balance in the name of rapid growth, not only increasing the probability of damage to themselves and their customers but whole industries.
How to protect oneself from identity theft.
- Check your credit ratings regularly. If any loans have been taken in your name, they will show up in the credit report. You can access this for free on CIBIL or Experian.
- Register for CDSL and NSDL Consolidated Account Statements (CAS). Any equity or mutual fund transactions done using your PAN will appear in this statement.
- Create a login on the income tax website and track the Annual Information Statement (AIS) for your PAN. The AIS provides complete information about a taxpayer for a particular financial year. Taxpayer’s income, financial transactions, tax details, bank accounts and large purchases (> Rs 2 lakhs), etc. The drawback with AIS is that it updates all the details only at the end of the financial year. Here is an FAQ on how to set up and use AIS.
- Keep a close track of all your banking and credit card transactions. Identities are stolen not just to create new accounts and loans that you are not aware of, but it is also used for conducting fraud using existing bank, mobile, credit cards, and loans as well.
- Do not reveal sensitive information on public channels and social media (accurate geographic location, mobile numbers, etc.).
- Finally, NEVER share account logins or SMS OTPs with anyone. No bank or the financial institution (or any legitimate institution for that matter) will ever call you and ask you to share OTPs or any sensitive details like card or bank account numbers.
Hopefully, you find this useful,

Request you to take this suggestion in Friendly manner. I am a new customer wish to open Zerodha. But your Video IPV verification by showing 4 Digit Number infront of camera is NOT good / NOT liked. I checked all other leading Share Broker’s Onboarding of 2 in 1 account in Youtube. Most of them are asking SELFIE PHOTO only. All other KYC due diligence are SAME as Zerodha. Your video IPV process is as disgusting as capturing criminals. Please change your Video KYC proceudre. Kindly follow what other share brokers are doing while onboarding the new customers. (i.e) Please Allow SELFIE PHOTO instead of Short Video. All customers are NOT criminals. Please read once again…. MOST OF ALL OTHER BROKERS ARE ASKING SELFIE PHOTO ONLY for IPV process. There is NO issue with all other KYC process such as submission of PAN, Aadhaar and so-on. Please change your policy in Onboarding of New Customers. Please REMOVE the short video IPV and proceed to permit SELFIE only as like as all other Share Brokers. Thanks !
Hi, Video IPV is no longer required while opening the account; you can proceed by uploading a selfie too. Currently, Video IPV is needed only when doing Re-KYC and we’re working on removing it too.
At the 7 step of esign the page is stucked at loading
Tried multiple times but its same
Pls let us know whats the issue
Is [email protected] a legitimate email address of address where you can send any required documents?
my adher card link to pan but my account is block
My account is still not activeted
What is going wrong?
Plz do active my zerodha account.
Hi Ashutosh, we’re sorry to hear about your experience. Please create a ticket at support.zerodha.com so we can have this resolved at the earliest. You can also contact us on our account opening helpline: 080 4719 2020.
https://zerodha.com/contact
Do active my zerodha account
Hello I am trying To open account and I completed step 2 and successful message also appeared but didn’t move to 3 step . What I should do?
Dear Sir/ Madam,
I have completed all stages upto e-sign. Still I haven’t yet received any mail for user ID and password. Kindly guide.
I have already linked my pan and adhar but my accounts shows not link so now how can I Trade in may account
Hi Hardik, sorry to hear this. If the PAN is already linked with Aadhaar, please create a ticket at support.zerodha.com so we can have this resolved at the earliest.
Bank to Zerodha account paroblab
Hey Sanju, please create a ticket at support.zerodha.com so that our team can check and assist.
Good afternoon
Thank you zerodha.
U people are best’ and transperant ,liked your kite software. Keep improving with more options of knowledge to invester.
I love zerodha for their services. Great going team zerodha
Very good.app. Excellent services.
I think excessive client load management is becoming a problem for zerodha
Zerodha is not able to satisfy it’s clients
Good
My zerodha account error not solve
(Modification not allowed after account opened) error
Please solved problem
Hey Yogesh, could you please create a ticket at support.zerodha.com so that our team can check and assist?
Nobody respond to our calls & mails.
how do i unsubscribe from emails that i get about my balance . i see no option to do so anywhere onbthe site
Identity theft is not a joke, Jim! Millions of families suffer every year!
Reduce brokerage charges
Activation of account
Hey Vinod, we’ve explained the process for reactivating the account here.
New customer, trying to exit from the screen, but, could not. Why comments needed?
Hey Vinod, please create a ticket at support.zerodha.com with more details so that our team can check and assist.
Nice..
I want to change my above mail id, how I can change, the above mail id I cant open, please help me in this matter.
Hey Sadanand, we’ve explained the process for changing your registered email ID here.
Good but why is Zerodha mandating us to provide a comment?
Good platform. Try to reduce Brokerage charges.
Very nice and efficient platform.
Yes, really good plarform but reduce brokerage charges.
Thank you!
Respected Sir,
Really good Platform but Please Reduce the brokerage charges..
Thank You
Good, happy to know we r safe with Zerodha
Good 👌
Good
I am really satisfied with your procedure for verification of client,,thankyou
Really good platform
Govt institution are giving xml based AADHAR AND PAN, SO no need to take uploads from Client for original pan and adhar copy.
Explore on this.
Very good future this app zirodha looking platform
Personally I like to use zerodha, it is very simple and easy, only one thing I don’t know still now, how to sell the share
Zerodha flatform is user friendly and more secure. Please permit more OTM to buy as hedging only, then it is supper for option sellers.
For banking transactions as detailed above IFSC Code and Account Number should be enough. Do you require MICR code by chance for any of the related purposes during security transactions?
👍
Good
Team,
very good support.
Thank you for alert and literate customers.
A good system followed, assuring good relationship with all concerned participants through security and curbing frauds.
Very bad
Sip amount not cut ,plz check and pls update.
Hey Suraj, please reach out to us on support.zerodha.com, so we can have this checked.
Very happy
Good afternoon safety client first I think my pan and Aadhar link your site.
KYC IS COMPLETED
we trust Zerodha for protecting our identity.
now I want to update my KYC with CKYCno.
What is the process?
Zerodha is Awesome platform
Good afternoon
Safety client first
I think my pan and aadhar link your site.
Most of the time my collogues have less margin compared to me for same option or future ..why it’s like this ? it should be across all zerodha account same right .
please clarify if anything
Hey Kumara, could you please create a ticket at support.zerodha.com so that our team can check and assist?
Zerodha is best but TOTP problem
Always happy with zerodha 😍
What about your own employees who sell customer data—-how this is protected ??
Very Nice . Thanks
Good explain good service
Good
Thanks always
Very happy with Zerodha
यह सभी पुराने लोगोंको भी करना है क्या सर
Very good app
I love zerodha team for creating awareness among retail investors and educating them..
what is the actions taken for the fraud login by someone into our account /portal – i have faced this issue 3 times even after changing the password -how this is possible
I have come across individuals charging 25k per daily insight/Crash course glidepath as well as prediction using Zerodha Name. who, shall I report?
Awareness is most important
Safety is first
Good
Good Experience With Zerodha
Good
चांगलं आहे परंतु कॉल घेतला जात नाही शेअर मार्केटमध्ये नवीन आलेल्या लोकांना काही एक माहिती नसते त्यामुळे ते मार्केट पासून दूर जातात म्हणून आपणाकडून त्यांचे फोन कॉल घेऊन त्यांचे अडचणीचे निवारण करावे ही विनंती
Good going. Account opened just last week. And have fresh memory of everything you have written. Feeling more secured against fraudsters. Kerp it up Bros.
Hi
But I know you do leak the personal information. I get numberous calls from stock brokers for trade where they tell me about my trades already done via zerodha. This information is either with me and zerodha. The point that they have this information means someone at zerodha gave them this information. This is very unprofessional
Hey Charan, we do not share client information with any third parties. We’ve explained this in detail here. Please report these numbers by following the steps given here.
Very good
I think my PAN is linked with Aadhar and u am getting my monthly and annual report from Zerodha
Still anything i need to do.
I have updated all the required documents with Zerodha as well.
Please take care my all investment Zerodha.
I know Zerodha is concern about customer safety but still please help me with the highest security please.
Good
Very nice 👌
Safety first
Very good and use full
Good Afternoon🙏,
Sir/Madam, I need Help to IPO information update immediately in this ✌Zerodha kite mobile apps in my Account id…… Ok 👌🙏✌👌🙏
Very Nice Thank you sir
Great app
If there is any best broker then it is Zerodha.
Sahi hai Security Is first priority
Hi … Thanks for alert…
Good
Very Good service
Zerodha is a really great platform , for trading as well as the systems they follow
Medium and satisfying experience
My Zerodha contact details shared to stock brokers. I have not given or shared mobile number to anyone. Only registered mobile number in Zerodha. How can we trust Zerodha?
Hey Venkat, we do not share client information with any third parties. We’ve explained this in detail here. Please report these numbers by following the steps given here.
Great
Great treding pathway of zerodha
Good
Very Nyc
This is definitely good.
nice
I’m complete KYC
But again KYC Complete
Very nice and thankyou for being so alert
Great app for Trading
This is definitely good.
My zerodha account is dormate plz activate my account.
Hey Nazeerul, we’ve explained the process for activating your account here.
What is this,koi batayega ye sab kya hai
Good
Good Experience With Zerodha…….✨
Nice features 👌 👏
SUPER TEAM
SUPER SIR
Awesome 👍🏻
your superb to protect customer
Good Services
Good app trading
Good app
This is fine.
But how do you store the client’s data? What if there is a leak of information of clients info. (PAN, adhar and bank info) to fraudsters. Hence the question. How do you store client information (encrypted or not) ? How many pepole have the access to this ? You are operating since 2010. I started getting pesky calls once I enrolled at Zerodha. When the a/c is closed, do you destroy or archive the data which no one could access.
Please comment.
Hey, we’ve explained the security practices we adhere to in this post. We do not share client information with any third parties. We’ve explained this in detail here. Please report these numbers by following the steps given here.
Ok…good job
I want to know the reason for blocked stocks especially of some penny stocks although the same stocks had been in my portfolio since long already. This restricts me to gain profit which disappoints me often.
Hey Chintan, you can trade in all stocks by enabling TOTP. We’ve explained the process for enabling TOTP here. We’ve explained the need for using TOTP here.
Good experience with zerodha
I am happy with zerodha service. Thank you.we need more support.
Great job
Good
Great app for trading…
Perfect
Learning & earning app
Hi, I’m satisfied with ZERODHA every active
Very good work but need to New update
It’s ok.
Since when Zerodha started giving loans?
Hey Saurabh, you can check out all information on Loan Against Securities here.
Yes
Excellent app
Perfect aap for the trader
Charts our good more than my expectations
What about your own employees who sell customer data, is it investigated?
There is huge loop hole in your own system.
Hey Rishikesh, we do not share client information with any third parties. We’ve explained this in detail here. Please report these numbers by following the steps given here.
noted steps taken to reduce frauds , will be more carfull in future
Hi I have good experience with zerodha
Perfect app for trade
Yes
Good App
Chart our well designed to trade
Excellent App
Awesome App
Good excellent
Hi
Ok
hi! i’m online! reply me if possible.
Very happy with zerodha
If Any Documents Issue pls Inform me
Nice platform
Zerodha You’re Good!
Hi , I m satisfied with zaridha for every activity 👍
Good app
Nice app thanks zerodha
Easy to use and easy to understand
Good application
Balance transfer to Bank takes long time. All n all good experience
Super work in zerodha tema
Hi
Safe
Zerodha ki karyapradali achchi hai
Great
Good
Good
Hii
ok
That’s fine. Highly appreciable
Nice
Nice
Good
Well designed to work with Zerodha
Zerodha is very good app
Ok
Ok sir
Good .Safety should be topmost priority.
Thanks Zerodha
Ok
Updated
Yes
Me myself trading
Good
Good Aapp
Login process is better if OTP process is included and do away with 6 digit pin system
good
Good
Happy
CLIENTS INFORMATION MAY BE LEAKEDBY SOME OF YOUR BROKERS. MANY OTHER STOCK BROKERS ARE ASKED FOR A/C OPENING
Great very simple to use
Good
What to do if my mobile is stolen where my dmat account is installed
I am very happy
Okay
Your luck in Your hand
am very happy with ZERODHA, I GAINED ALOT OF KNOWLEDGE WITH VARSITY AND TICKERTAPE
Best aap
When are far options going to start on zerodha?
Good
Must required
Stock market=Zerodha
Great
Good important information, I am safety.
I want to check my PAN NUMBER linked with LIC policy
Hey Sateesh, we’ve explained the process here.
I am happy open to account thanks e support. Mi
Hi
Please give excess usa treading.
Ok
I am happy with Zerodha services and i gained lots of knowledge of things what can work in the share market.
Problem solved
Hi
Ok
Dawar
I am very happy
Nice
Hi
Good very very good and happy till date
Haii
Very much required
Ok
am very happy with ZERODHA, I GAINED ALOT OF KNOWLEDGE WITH VARSITY AND TICKERTAPE
Ok
Good
Thanks for reassuring my belief that Zerodha is customer centric.
good
Best service
N.A.
Thanks for being vigilant
You are bestest. !!!
Hiiii
Hii
yes
I am
Not opening phone aplication able
Hey Visrut, we’ve been working fine. Please create a ticket at support.zerodha.com with more details so that our team can check and assist.
i am unable to by option trading plz rectify it
You have to unlock option and future segment for this
Please strat my future and options ………..my account balance is 27830.73 but my future and options is blocked
Hey Rajendra, we’ve explained the process for activating the F&O segment here.
Go to Zerodha console and activate derivative segment for your account by providing some details.
i am very happy with ZERODHA, I GAINED ALOT OF KNOWLEDGE WITH VARSITY AND TICKERTAPE
Achha hai. Safety first.
बहुत खूब। समय के साथ आगे भी सुधार करते रहिए।
धन्यवाद
very nice good
Awsm… okey..